Tech Tuesday: Identity theft prevention best practices recommended
From Information Resources and Technologies
Those Citibank ads with the victim acting to the perpetrator's voiceover are a funny way to look at what can be the very serious problem of identity theft.
Identity theft can happen in a variety of ways: someone pilfering your wallet or laptop, going through your garbage to retrieve sensitive documents, or even someone impersonating you online. The best way to protect yourself against becoming a victim of identity theft is to use "best practices" in your everyday computing activities.
Here are some examples of common best practices:
- Secure your physical assets by locking up your laptop and locking your desktop session when you walk away from your computer.
Physically locking your laptop may seem like an obvious and trivial way to prevent theft, but identity theft is made very easy when the laptop is in a criminal's hands. Also, when you walk away from your computer, whether it is in your office, in your dorm room or in the library, you should always lock the session when you're away from the computer. If you can't lock your operating system, you should set the machine so that the screensaver activates automatically and has to be unlocked using a password. In the case of going to the library, bring a cable lock just like you would with your bicycle to secure your laptop.
- Store all data on network and e-mail as much as possible.
Storing all your data on UST network storage locations provides multiple advantages regarding data security. The obvious advantage is that you cannot lose your data – even if you were to delete it intentionally, it can be restored because network and e-mail servers at UST are backed up nightly. You can overcome the loss of data by physical or software malfunction, theft, damage or loss of your entire computer simply by using these network storage solutions. Also, any data stored in these locations is tied specifically to your UST network identity. In addition, note that it is important not to store sensitive data on a USB drive, as they tend to get lost easily.
- Use password layering and complexity (e.g., don't use the same password for different accounts and sites, don't use birthdays or easily guessed names within passwords).
Using strong passwords and good password security sense goes a long way at thwarting identity theft.
Here are the characteristics of a strong password:
• Over six characters,
• Does not contain words, and
• Has a random mix of alphanumeric and symbol characters.Password "layering," or the idea that you should have different passwords for different services, is also an important aspect of data security. Ideally, you would use a different password for every different service that requires one. This is hard for most people to do but, as an example, you could use one password for your online banking that is separate from all your others. This way if your hotmail password became compromised, other important information would remain secure.
- Don't store passwords in Web browsers, or toolbar utilities, etc.
Storing passwords in a Web browser can be a lot like storing the password on a Post-it on your desk. And storing passwords on a Post-it note is very much like storing passwords in a glass window on Nicollet Mall during the lunch rush. Anyone who happens by the Post-it note will see it, just as anyone who may gain access to your Web browser would have access to whatever log-ins and secure sites you have stored.
- Don't share information on the Internet that you want kept private.
A step toward keeping data private is developing a better understanding of what data is easily accessible electronically. Generally, anything posted on a Web page is easily accessible. If you post a phone number on your Facebook profile, for instance, almost anyone has the potential to gain access to that number. The same concept applies to MySpace and Instant Messaging profiles and automatic "away from the keyboard" messages.
- Don’t fall for Internet phishing schemes. Never follow e-mail links to Web sites unless you know 100 percent for certain that it is a legitimate site.
If you receive a link to vote for Tommy of the Year, it's probably safe to follow it; however, never respond to phishing attempts from what appears to be eBay, PayPal, Chase VISA, etc! Following a link from a phishing scheme e-mail collects your username and password for any given electronic service. It also may provide an opportunity for malware to be installed onto your computer. Generally speaking, even if the e-mail is from a company with which you have an account, you should never respond to it; the rule of thumb is that reputable businesses never ask for personal data to be transmitted via e-mail.
- Use transmission encryption (SSL, TLS, PGP and WEP) and physical encryption (file and full-disc encryption, especially with USB drives).
Encrypting data, so that it cannot be read by anyone except for those for whom it is intended, is an invaluable security measure. While data encryption is not used widely by the average person, it will become more and more important in the near future. Data encryption happens in two ways: transmission encryption safeguards data from point to point, while physical encryption safeguards stored data. When you log in to your bank's Web site, encryption tasks depend upon a Secure Socket Layer (SSL) in the browser. Pretty Good Privacy (PGP) is one of many software packages that can be implemented to allow e-mail transmission to be encrypted. Wireless Encryption Protocol (WEP) protects the information packets sent between your wireless device and the wireless access point. Currently, the wireless networks at UST do not use any encryption, to allow for maximum compatibility with a wide variety of wireless devices, and rely on the browser's SSL for encryption tasks.
Physical encryption is either at the file level or the disk level. At the file level, you could use either the Windows or Mac's built-in systems to encrypt files – basically, it is akin to password protecting a document. Disk level encryption allows the entire storage volume, let's say, a hard drive or a USB drive, to be protected in the same manner. If you were to lose such a drive, the finder would only encounter the encrypted data as a garbled mess and could only format it, protecting the integrity of your data.
- Be security-minded by keeping operating system, anti-virus, and anti-malware programs up to date.
Installing manufacturer-recommended updates and patches helps protect your computer from previously known and recently discovered ways of compromising data security. Installing these fixes is one of the easiest ways to provide peace of mind.
While an event of physical identity theft is going to be realized almost immediately, a data theft might only be realized once the bills come. Following these eight "best practices" will help you prevent your data from being compromised. And as most things go, an ounce of prevention is worth a pound of cure.
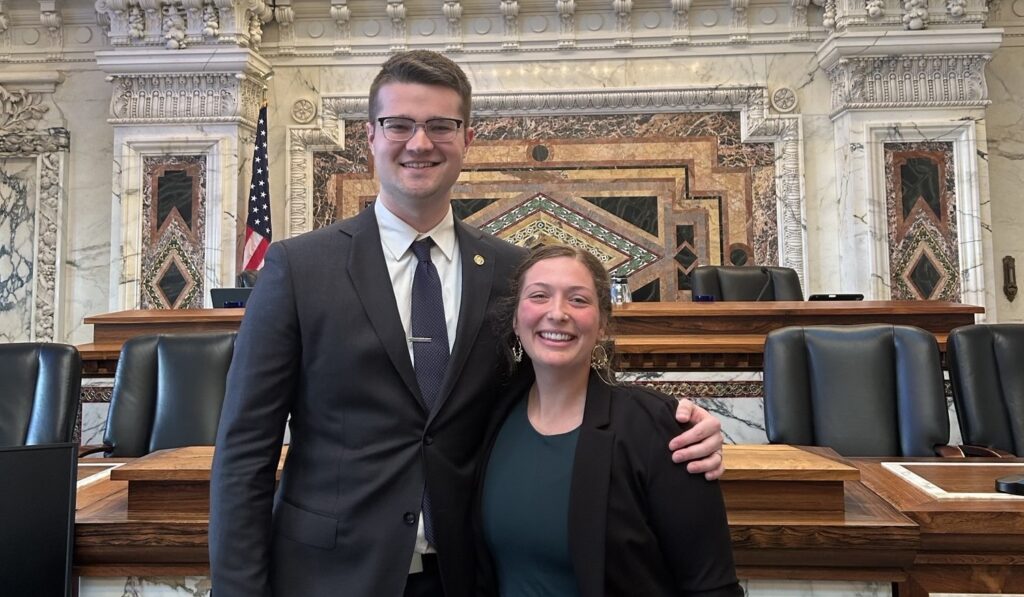
These identity theft tips have been provided by Information Technology's Kaleb Sargent and Client Services' Michael Sheehan and Jess Walczak.
If you have questions about any of these identify theft best practices, contact the IRT Tech Desk, (651) 962-6230.